This is the first of a series of articles related to OWASP TOP 10 under .NET technologies
INTRO
In this series of articles we are going to review OWASP TOP 10 most critical web application security risks under .NET applications perspective and I´ll try to show how to use .NET native defences and patterns for preventing them as far as possible…, because the reality is that software development frameworks (with no exception for the .NET one) are insecure by default, even more, as it will be seen later, sometimes there is no possible to correctly mitigate some risk using built-in framework common defences, for those cases we need to implement third-party products for helping to reduce risks
A Little About OWASP
OWASP is the Open Web Application Security Project, founded at the end of 2001 as not profit international organization and open community “dedicated to enabling organizations to conceive, develop, acquire, operate, and maintain applications that can be trusted”. In this line, OWASP tools, documents are free to anyone interested in web application security. They don´t make money from out of anyone, the only purpose is to contribute to make the web a safer place. OWASP principles are technology agnostic. They don´t promote any specific technology, and they are not affiliated with any technology company so OWASP principles and concepts span to different technology stacks like Java, .NET, PHP, etc…
OWASP Top Ten
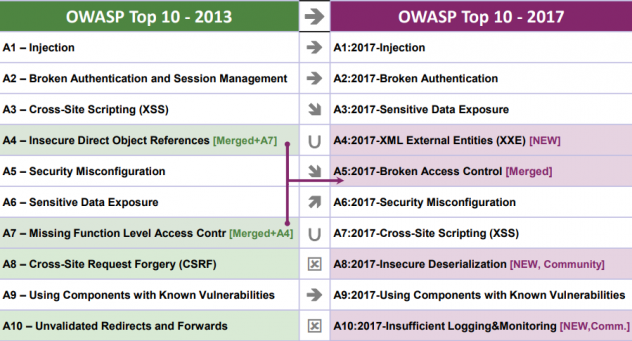
Owasp Top 10 is an awareness report (which is updated in a regular basis) about web application security that lists top 10 most critical security risks according to wide broad consensus from security experts about the world. This document represents a solid reference for web application security and OWASP urge companies to adopt it for minimizing security risks. Is a matter of fact that as software becomes more complex and interconnected more difficult results to protect it, so it becomes essential to have a guide for supporting web application security challenges
So OWASP Top 10 can be seen as a set of standards for securing web applications that companies can adopt for increasing security of their software. At the same time, this document represents a valuable reference for developers to build secure software which is no so common when building our applications. Security professional often use also OWASP when assessing application security by using pen testing tools
Real Threat
Consequences of web-attack should not be underestimated; according to Gartner about the 85% of web sites have serious security flaws, so it becomes imperative the diligent implementation of defensive design and coding. Attackers can have different motivations, experience and resources (hacktivists, on-line criminals, and even nation states) , so architects and developers need to be aware about security when building web applications. Following are only a little sample of known companies who have been hacked in recent years :
From Here
In following articles we will review each of them by providing specific code samples and showing how to implement .NET native defences for mitigating those risks (at least in some cases) :
- Owasp Top 1 : Injection Basics
- Owasp Top 2: Broken Authentication & Session Management
- Owasp Top 3: Sensitive Data Exposure
- Owasp Top 4: XML Extenal Entities (XEE)
- Owasp Top 5: Broken Access Control
- Owasp Top6: Security Misconfiguration
- Owasp Top 7: Cross Site Scripting
- Owasp Top 8: Insecure Deserialization
- Owasp Top 9: Using Components With Known Vulnerabilities
- Owasp Top 10: Insufficient Logging & Monitoring

